Documenting The Gross Incompetence, Complacency and Ignorance of Monero Research Labs Devs
A lot of maybes worth pondering, MRL
It’s always very difficult to determine exactly how much certain high profile developers know about the tech they supposedly contribute to. Do they know and don’t speak for fear of being cut out of their funding club, or do they simply NOT know? Well, I could answer this myself but, again, I don’t want you to take my word for it. Instead, I was able to find a Reddit thread from October 2022 where a lot of MRL contributors and developers participated in a discussion on the pros and cons of the account model vs UTXO.
The top comment everyone agrees with
The creator of the thread (who deleted it after posting) basically suggested that everyone look into Dero and its account model because it has some privacy and scaling advantages. Now, in my experience, this is a recurrent theme in Dero. You see a lot of alpha/deep insights about Dero dropped around like this by people that have later deleted their threads. As if they were just testing the audience, or borderline trolling, or in an attempt to document for posterity the ignorance of certain people at the time of writing. Or maybe, simply because Dero turned out to be an inflation scam (who knows). Anyway, this is the top reply in the thread:
Dero’s account based model has significant drawbacks:
Monero uses stealth addresses to for recipients, which are indistinguishable. Dero uses a ring, so it’s 1/16.
Much greater statistical analysis via long term data accumulation and interaction frequency.
Is Kayaba right? Let me break down again how Monero works for you so you can decide on your own.
For any Monero transaction, when Alice wants to send 1 XMR to Bob, Bob has to give Alice his public address. Bob’s public address is then used by Alice’s wallet to create a new output for Bob that only Bob can spend. This new output will have its own destination address which is engraved onchain, together with a Pedersen Commitment attached to it, a cipher that hides the balance contained in the output.
This is how all Monero “stealth” addresses are created, they are simply outputs created by senders that can only be spent by the receiver. Now Kayaba says that these outputs are superior to Dero’s accounts because they are indistinguishable/fungible.
Are Monero outputs more fungible than Dero addresses? They are not more fungible for the reasons I will list below and the root cause of all these reasons is the fact that Dero uses El Gamal (+ account model), which is both public key rerandomizable and public key updatable. While Monero uses PCs (+ UTXO), which cannot be updated or re-randomized.
Monero outputs are single use (because PCs cannot be updated), meaning that they can be spent only once and once spent they’re dead. This, when combined with the UTXO accounting model opens the door to many heuristics that completely destroy fungibility and can be used to systemically kill privacy just by analyzing onchain activity:
Recency Heuristic (much weaker on Dero): In Monero I can tell exactly when was the last time that an output was “updated”. That is the time when the output was created, ie when the sender of some transaction created it and put a certain balance in it. This forces the recency heuristic on all Monero outputs present onchain. In Dero, contrary to Monero, once an account participates in a single transaction, I can no longer tell whether it was updated or just rerandomized. This is because El Gamal is rerandomizable. Due to this the recency heuristic is much weaker.
UTXO Heuristic (non existent on Dero): Because of the UTXO accounting model, and because of the fact that every incoming transaction creates a new output in receiver’s wallet, a Monero transaction has a UTXO footprint that consists of the number of outputs being spent (number of key images) and number of new outputs being created. This makes the outputs created by these transactions non fungible. For example, is the output created in a 10-to-1 transaction, fungible with the output created in a 10-to-20 transaction? No, because just by the UTXO structure we can tell that 10-to-1 is likely a consolidation transaction (ie: coins didn’t exchange hands), while 10-to-20 is likely a payout transaction output (eg: belonging to a mining pool customer). In Dero there is no UTXO heuristic because the entire encrypted balance is attached to one address, that of the Dero account, and is updated after every transaction. In each transaction the spender forms a ring with other accounts present onchain, the ciphertexts of all of which are rerandomized.
These 2 heuristics alone provide enough basis to refute Kayaba’s claim that Dero’s account model has significant drawbacks. Because, as shown here, outputs are NOT indistinguishable and the UTXO model plays a key role. The lack of fungibility can then be exploited systemically (fatally) to break Monero rings with methods such as cluster analysis:
When multiple outputs from a narrow time frame, say within 20 minutes, appear among the inputs of the same transaction that indicates that they’re being spent in that transaction.
When multiple outputs sharing the same UTXO fingerprint (such as many-to-one or one-to-many) form clusters then again they can be exposed as the real spends in those transaction with a margin of error that is astronomically low (less than 1 in a trillion) and can be narrowed further by cross referencing fee behavior.
These heuristics canbe expanded inductively to brute force rings by filtering out outputs that are known to have been spent.
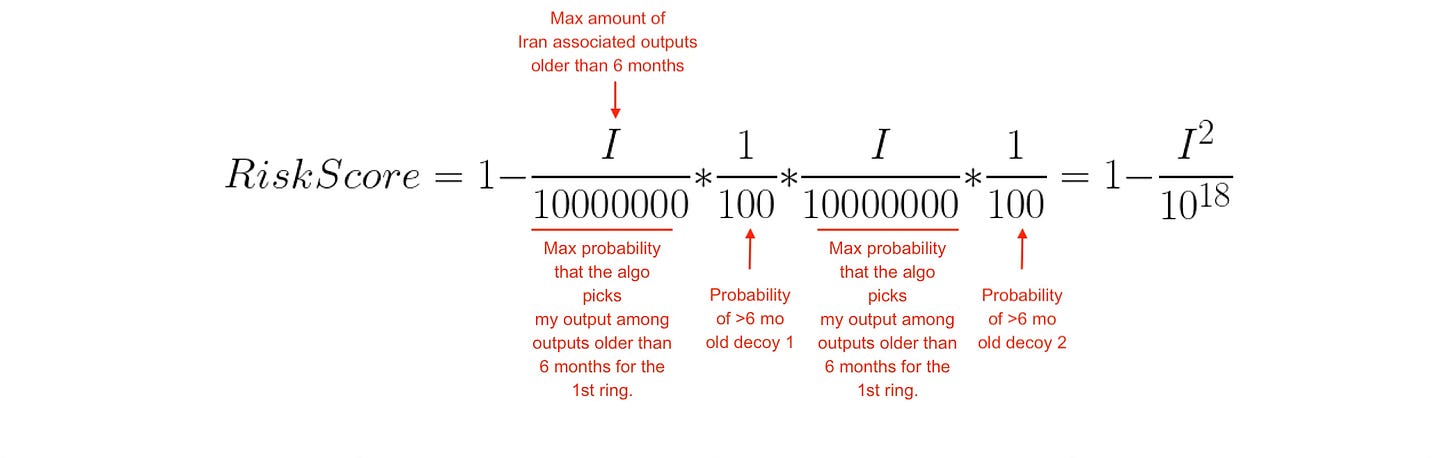
How much weaker are account model heuristics in Dero compared to UTXO heuristics in Monero? Let’s do the math with a real life example.
Let’s say I’m a new crypto user who has $5 in my Dero wallet and $5 in my Monero wallet. Let’s say I’m from Iran and I’ve accumulated this balance from local crypto users who tipped me small amounts as part of an onboarding initiative. And today, after 6 months, I want to pay a merchant that I suspect could exchange information with the Iranian government if they suspect a payment to be coming from Iran.
And for the sake of the argument let’s also assume that the merchant has a Chainalysis subscription that gives them access to a database that has indexed both my Dero address and some Monero outputs as likely linked to Iran because of the frequent Iranian IP.
Now, am I safer paying $5 (eg: for my VPN subscription) with Dero or Monero? Let’s calculate a “risk score” for both transactions, where risk score is defined as the likelihood that the transaction I conduct is attributed to a user in Iran.
In Monero’s case there are about 27500 transactions per day today, which means at least 10M new outputs every 6 months (assuming 2 outputs per transaction). The decoy picking algo currently has a probability of less than 1% of picking an output that is older than 6 months. In the Chainalysis radar my transaction will feature:
At least 2 outputs from over 6 months ago (possibly more if they all came through tips)
The pool of outputs older than 6 months is at least 10M
Let’s mark as I the amount of Iran associated outputs indexed by Chainalysis every 6 months
The absolutely minimum probability that my transaction was not random but intentional (therefore Iranian outputs are being spent) is at least:
Numerically, for I=10000000000 (for a state where ~1% of outputs are Iranian), that’s at least 99,9999999%, ie 100%. If the amount of Iranian outputs is less than 1% (which it is), the risk score goes even higher, although it’s already extremely high.
This probability is calculated assuming Chainalysis is a passive observer and isn’t spamming the chain with any outputs to poison rings. So by default, the Monero blockchain itself, because of its UTXO accounting model, single use outputs, and the heuristics that follow, exposes the sender with 99.99999999% certainty. If the transaction consumes even more outputs then the risk score increases further.
Now let’s calculate my risk score if I use Dero for my transaction. Like Kayaba states in his comment, if I use Dero with a ring of 16 members then Chainalysis will see that the payment contains 1 account associated with an Iranian user. Since all ring members in a Dero transaction are perfectly fungible because all ciphertexts get rerandomized, the risk score defined as probability that my Iran associated output is the real spend will be exactly 1/16.
Again, this is a probability from a passive observer’s point of view. The highest probability the network leaks is 6.25%.
Therefore the math confirms that the most private payment method is by far Dero (Account model with El Gamal), not Monero. Notice also how in Dero’s case the total number of accounts onchain is irrelevant, since contrary to Monero accounts are updatable and not single-use. The fact that user balances are split in different outputs (“stealth addresses”) is what ultimately kills Monero’s privacy in practice because when compounded with other heuristics it leaks the real spend with an astronomically low margin of error.
“Much greater statistical analysis via Long Term data accumulation”
This part of the comment is another embarrassing display of incompetence. In Monero, because of the UTXO model, we can conduct cluster analysis which exposes the real spend of various transactions and with time we can compile a huge database of these dead outputs that are known to have been spent. Next comes passive brute forcing of transactions with time since we would be able to filter out decoys of other transactions once we find out where an output is spent. This would expand our transaction graph further.
Contrary to Monero, in Dero accounts remain updatable for life because they use El Gamal. Therefore long term statistical analysis actually becomes harder not easier as it becomes increasingly harder to tell whether an old account has resumed spending or was casually picked as a decoy after a long time.
In other words, the account model does not leak any patterns in Dero that would allow an analyst to construct any fragment of a transaction graph.
Maybe it’s time to wrap it up
Maybe most of Monero’s devs today are out of depth and they don’t really understand the tech well enough to be working on privacy. Maybe their understanding is too narrow, too local and too blindsided by their greed for grants. Maybe they should humble down and leave a stage where they obviously don’t belong. Maybe there is a group of much bigger experts out there that has opted for Grand Silence so you can irreperably make a fool of yourselves and never again say you knew. Maybe they are laughing their asses off in the shadows while you make a fool of yourselves.
Just saying, you know. Think about it.